您是否认为从搜索引擎获取结果,就像从 A 连接到 B、从您的设备连接到 Web 服务器一样简单?不,许多隐藏工具会检查您的流量并确保您的网络安全。网络地址转换或 NAT 防火墙就是这样的一种工具,一般是安装在路由器上。
什么是防火墙
要了解什么是NAT防火墙,首先需要了解什么是防火墙及其作用。最简单的比喻是:如果电脑是忙碌的 CEO,那么防火墙就是 CEO 的秘书。这个秘书对邮件进行分类,确保唯一通过的邮件就是 CEO 真正想要的。
在线浏览、发送电子邮件或在线观看电影时,会向特定网站服务器发送信息请求。防火墙位于本地网络和更广泛的网络之间。防火墙将返回的信息与请求的信息进行比较——匹配的所有信息都通过,而它无法识别的所有信息都将被丢弃。这样,防火墙可以保护免受不请自来的恶意互联网流量的侵害,否则这些流量可能会试图危害您的系统。
防火墙大致可以分为三类:软件、硬件和基于云的解决方案。不同的防火墙也应用不同的过滤方法,这使得它们比其他防火墙更可靠。
相关:什么是防火墙
什么是 NAT,它的工作原理是什么
NAT是 Network Address Translation ( 网络地址转换 ) 的首字母缩写,是解决 IPv4 协议带来的一个问题:IP 地址短缺。过去,IPv4 的创始人认为, 43 亿个 IP 地址足以满足所有联网设备的需求。然而,考虑到世界上有超过 70 亿人,而且许多人拥有不止一台设备,很明显没有足够的设备来满足需求。
那么,NAT防火墙究竟是什么
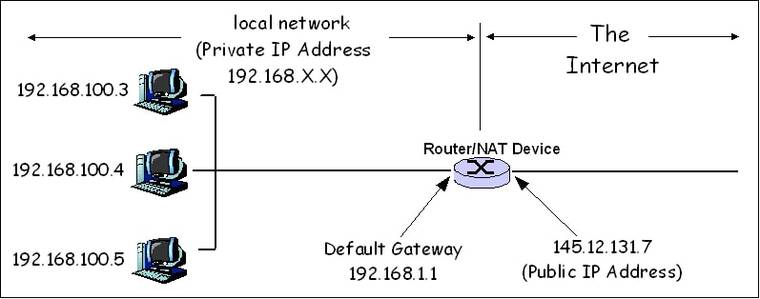
网络地址转换 (NAT) 防火墙 是网络设备(通常是防火墙)为专用网络内的计算机(或计算机组)分配公共地址的过程, 在路由器上运行以保护专用网络。 NAT 的主要用途是为了经济和安全目的,限制组织或公司必须使用的公共 IP 地址的数量。
NAT工作原理是:仅在专用网络上的设备请求时才允许互联网流量通过。 NAT 防火墙保护网络的身份,不会向 Internet 显示内部 IP 地址。
这是因为,当连接到 Internet 时,路由器会被分配一个公共 IP 地址。它对更广泛的网络可见,并且需要与 Web 服务器进行通信。本地连接到路由器的任何设备都有私有 IP 地址,这不允许它们直接与所需的 Web 服务器“通信”。这就是 NAT 发挥作用的地方——它来回引导流量。
NAT 防火墙如何工作
最常见的网络转换形式涉及使用专用范围(10.0.0.0 到 10.255.255.255、172.16.0.0 到 172.31.255.255 或 192.168.0 0 到 192.168.25)中的地址的大型专用网络。私有寻址方案适用于只需要访问网络内部资源的计算机,例如需要访问文件服务器和打印机的工作站。专用网络内的路由器可以毫无问题地在专用地址之间路由流量。但是,要访问网络外部的资源,如 Internet,这些计算机必须有一个公共地址,以便对其请求的响应返回给它们。这就是 NAT 发挥作用的地方。
- 设备通过发送数据包向 Web 服务器发送请求。这些数据包包括诸如发送方和接收方的 IP、端口号以及请求的信息等信息。
- 流量通过带有 NAT 防火墙的路由器。 NAT 将数据包的私有 IP 更改为路由器的公共 IP。它记录此更改并将其添加到其 NAT 转发表中。
- 数据包到达网络服务器并获得必要的信息。
- 信息传回到路由器。现在 NAT 的工作是将信息发送回请求它的设备。否则,每个连接的设备都会收到相同的信息。 NAT 使用其转发表来确定谁请求了此数据。
- NAT 将数据包的公共 IP 更改为其先前的私有 IP,并将其发送到请求的设备。
NAT 如何保护您
NAT 可用作硬件防火墙解决方案, 但是NAT并不是安全工具,那么它如何保护的呢?
- 它向外界隐藏网络上任何设备的 IP 地址,为它们提供一个单一地址。
- 它要求设备要求每个传入的信息包。如果恶意数据包不在预期通信列表中,则会被拒绝。
- 某些防火墙可以使用白名单来阻止未经授权的传出流量,因此如果确实感染了一段恶意软件,防火墙可能会阻止它与设备进行通信。
更复杂的攻击可以NAT,尤其是那些采用网络钓鱼或社会工程方法的攻击。但是,这并不意味着不应该使用NAT。如果没有 NAT,任何业余黑客只需了解 IP 地址就可以轻松访问计算机。
NATs 与 VPNs
有些人认为 VPN 不应与 NAT 一起使用。为什么? VPN 在您的流量到达互联网之前对其进行加密,使其无法破译。 NAT 需要了解有关该流量的一些信息才能完成其工作。过时的 VPN 协议(PPTP 和 IPSec)无法向 NAT 提供足够的信息,因此可能会被阻止。要解决此问题,路由器需要 VPN 直通。
好消息是大多数路由器都有内置的 VPN 直通。即使不这样,大多数流行的 VPN 提供商也会提供不需要直通的更高级的协议。例如,NordVPN服务器 不仅不再使用这些过时的协议,而且使用内置的 NAT 防火墙。